Policy & LawGlobal Supply Chain Crisis: Iran Conflict Escalates with Cyberattacks and Shipping Disruptions
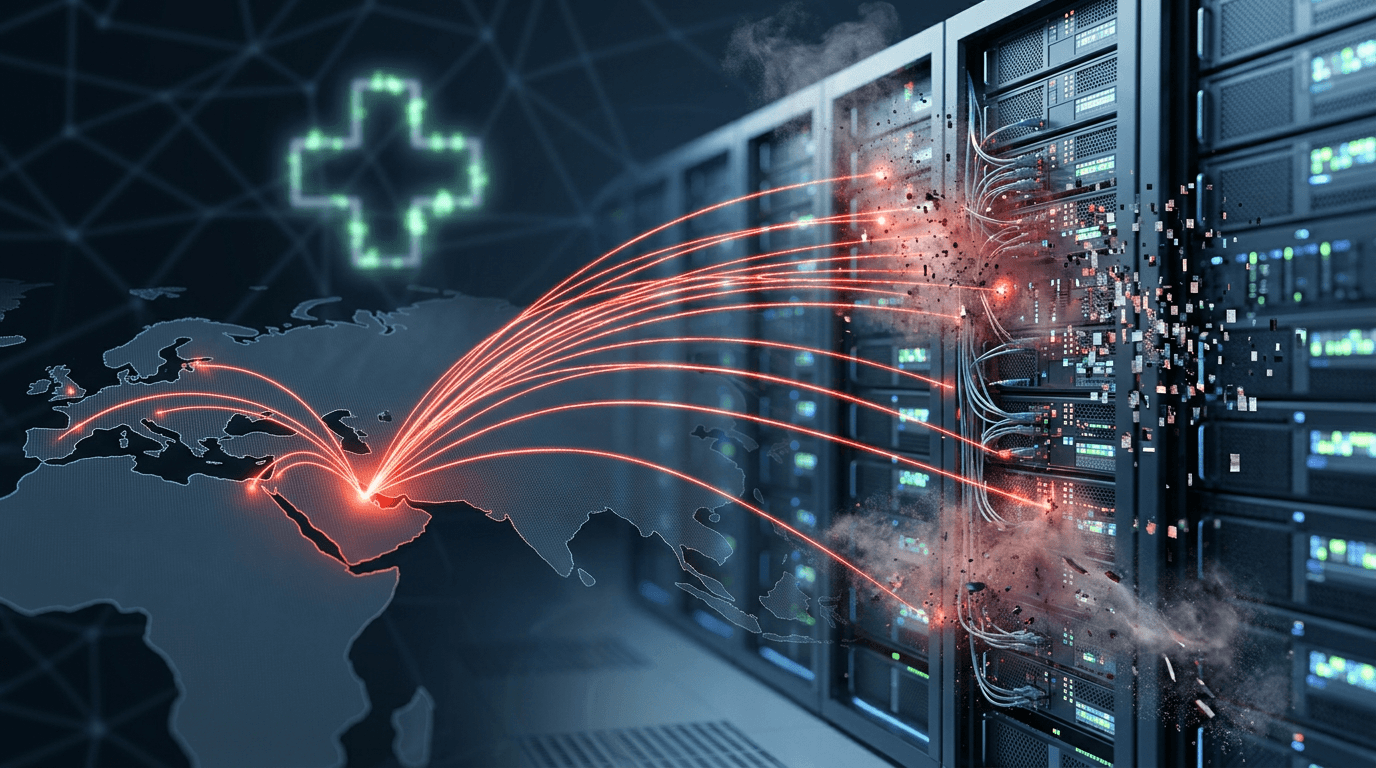
The conflict involving Iran has transformed into a global systemic crisis, combining destructive cyberattacks with physical disruptions to shipping. The U.S. has linked the Iranian government to the 'Handala' group, which recently targeted medical giant Stryker and disrupted vehicle breathalyzer systems across the U.S. Simultaneously, threats to maritime routes have paralyzed Red Sea shipping, pushing energy markets toward a worst-case scenario. This multi-front hybrid war is exerting massive inflationary pressure on the global supply chain.
 Kenji··3 min read
Kenji··3 min read