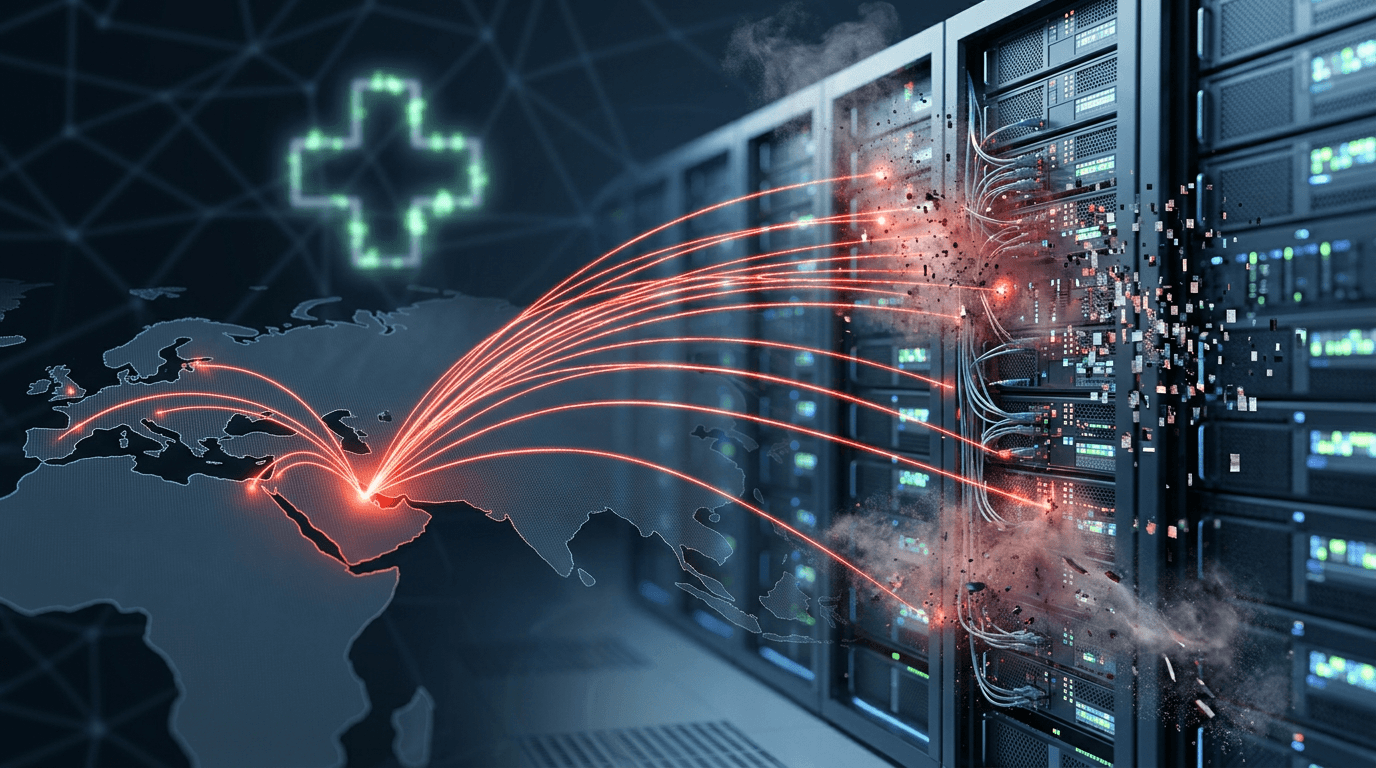
Medtech Giant Under Siege: Total Windows Network Failure
Stryker, a premier global supplier of lifesaving medical devices, is currently grappling with a devastating cyberattack that has completely paralyzed its Windows-based networks. As reported by Ars Technica, the company fell victim to a 'wiper' attack—a malicious category of software designed to permanently destroy data. Given Stryker's pivotal role in the global healthcare supply chain, this disruption goes beyond corporate loss, posing a potential risk to hospital operations worldwide. The company has admitted it remains uncertain about the timeline for restoring its Microsoft environment.
Unmasking 'Handala': Hacktivism as a State Cover
The group claiming responsibility, known as 'Handala,' has emerged as a significant threat actor in the context of recent Middle Eastern conflicts. Wired's investigation reveals that Handala frequently operates under the guise of 'hacktivism,' utilizing war memes and political rhetoric to cloud its true origins. However, cybersecurity analysts believe the group serves as a front for Iranian state-sponsored operations. By using hacktivism as a cover, state actors can launch chaotic, retaliatory strikes while maintaining plausible deniability—a strategy that is becoming a hallmark of modern cyber warfare.
Legal Implications: SEC Disclosures and HIPAA Compliance
The breach at Stryker triggers a cascade of regulatory requirements. Under the SEC's 2023 Cybersecurity Disclosure rules, publicly traded companies must report material cybersecurity incidents within four business days. More critically, as a major player in the healthcare sector, any potential compromise of patient data could lead to severe penalties under the Health Insurance Portability and Accountability Act (HIPAA). The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has designated the Healthcare and Public Health (HPH) sector as a high-priority target, likely leading to intensive federal oversight of Stryker’s recovery efforts.
International Law: Crossing the Threshold of Armed Attack
This incident adds a new layer to the debate over international law in cyberspace. According to the 'Tallinn Manual 2.0' framework, state-sponsored cyber operations against critical infrastructure can, in certain circumstances, be interpreted as a violation of sovereignty or even an 'armed attack.' While no physical casualties have been reported directly linked to this breach, the systemic disruption of medical supplies sits in a legal grey area that could justify international sanctions or counter-measures from the U.S. and its allies.
Future Outlook: The Weaponization of Wipers
The attack on Stryker is a grim reminder that corporate networks are the new frontlines of global conflict. 'Wiper' malware is increasingly being weaponized to cause maximum economic and social disruption rather than just data theft. Experts predict that as geopolitical tensions simmer, critical infrastructure—particularly in healthcare and energy—will face more frequent and sophisticated 'hacktivist' fronts for state actions. Companies must now prioritize 'cyber resilience' over simple defense, assuming that a breach is not a matter of 'if,' but 'when.'