Policy & LawCyber Frontlines: US Dismantles 3-Million Device Botnet as Healthcare Tech Faces Iranian Cyber Assault
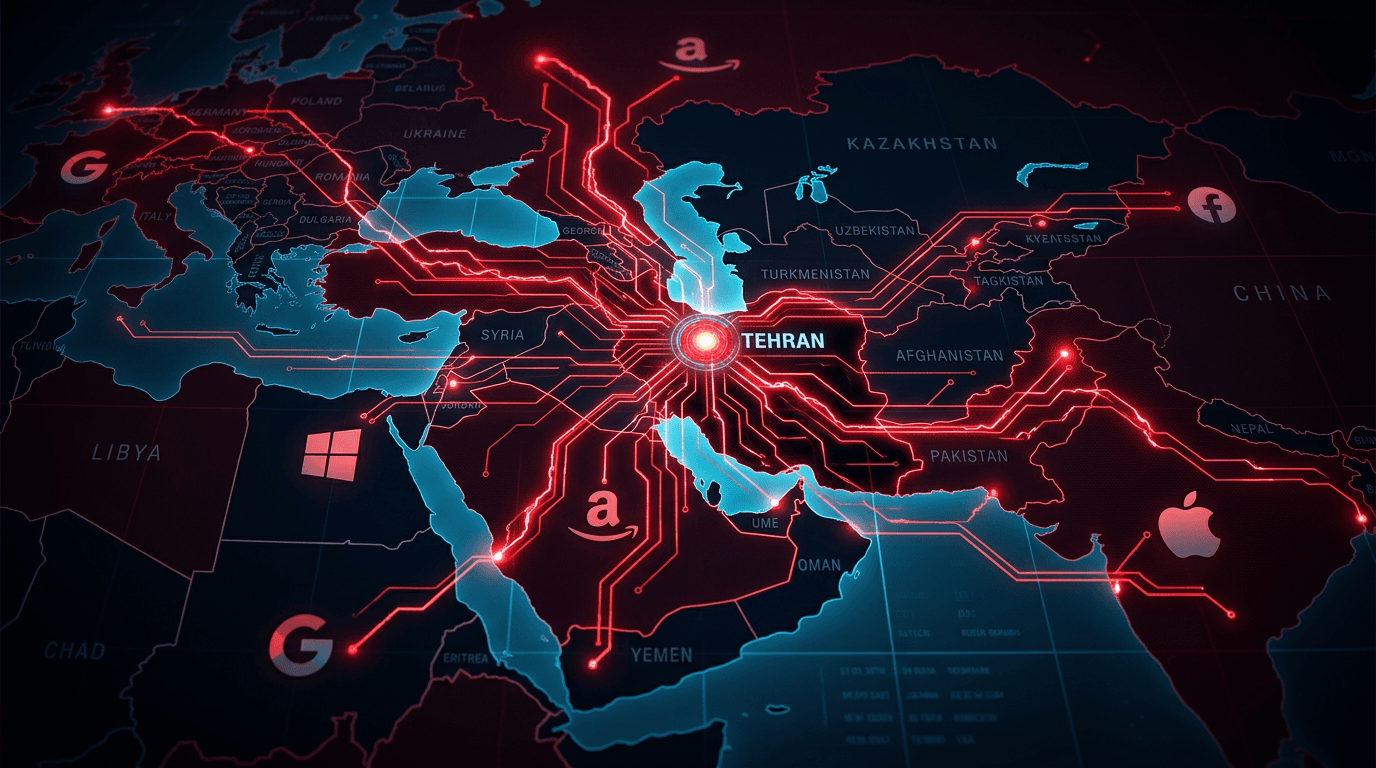
In March 2026, the U.S. DOJ dismantled four botnets affecting 3 million devices. Simultaneously, medical giant Stryker suffered a devastating 'remote wipe' attack by the Iranian-linked group Handala, which exploited Microsoft Intune to reset thousands of devices. The FBI and CISA responded with domain seizures and urgent security warnings, highlighting the intensifying nature of global cyberwarfare in the healthcare sector.
 Jessy··3 min read
Jessy··3 min read